Firewalls are a critical part of today’s cybersecurity efforts. They are indispensable when private networks try to separate themselves from the threats on the Internet and control the flow of traffic on their systems. But not all firewalls are designed the same, there are a plethora of firewall types and you need to choose the right one for your business.
In this article, we will try to explain the different firewall types you can choose from, and help you understand their main functions and purposes. This will simplify the process of choosing a firewall solution and in general, give you a better idea of how these tools work.
Introduction to Firewalls: Why Your Business Needs One
A firewall, in essence, is a digital wall placed between your network and the unpredictable, insecure world of the outer Internet. Its primary mission is to always watch and control the incoming and outgoing traffic in the network to only allow authorized information to go through. This means that firewalls have a set of policies that they use to decide whether they will allow something or not.
Why a business would need a firewall? Well, firewalls would be your network perimeter, so it’s the very first thing you can use to prevent cyberattacks and data breaches. Without a firewall, you would be risking your network at all times since it will basically be intertwined with the external Internet. A firewall, on the other hand, ensures that your private network stays private.
Content
Understanding Your Business’s Cybersecurity Needs.
Before you evaluate any of your firewall options, start by understanding your business’s cybersecurity needs as they will be the primary reason why you’re choosing a firewall solution. The best way to do it is to review the current state of your network, understand the threat landscape, and consider the weak points in your systems.
It is also highly important to see what kind of data you are handling on the network and decide the level of security they need. Categorizing the data on hand will also be useful when you implement access management for better internal security.
Furthermore, staying ahead of industry trends and emerging threats is crucial. Cybersecurity is a dynamic field, and threats continually evolve. Regularly reassess your needs to ensure your chosen firewall remains effective in mitigating the latest risks.
Hardware vs. Software Firewalls: Which is Right for Your Business?
When you are choosing a firewall solution, you need to decide on one significant thing; hardware or software firewall. There is not a one-for-all answer to this question, and both have their advantages as well as downsides.
Hardware firewalls are physical devices placed on your data center, and they become the barrier between your network and the Internet. They offer centralized management for all the devices involved, and they give more control to the organization over the firewall. This is why hardware firewalls are better suited for larger organizations. But you need to keep in mind that their setup is complex and maintenance is ongoing.
Software firewalls, on the other hand, are software applications installed on devices individually. This can either be end-user devices such as work computers, or network devices like routers. These solutions are provided by third parties, but they offer granular control so you can customize them for your needs. Software firewalls are especially great for remote work as they can go where the user goes, but managing and updating multiple firewalls on multiple devices can be challenging.
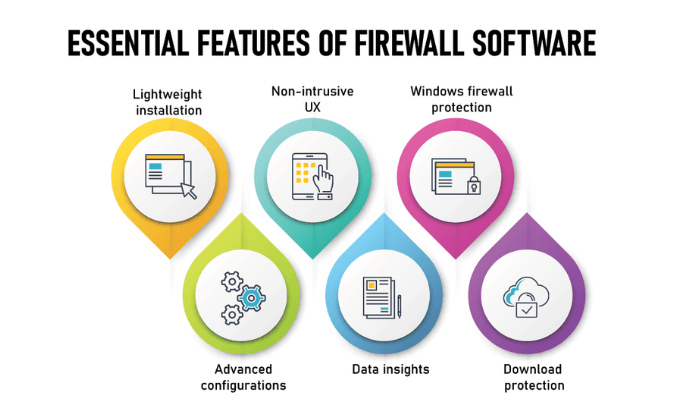
Evaluating Firewall Features: What To Look For
You need to check the variety of features a firewall offers before investing in it. These features should meet your business needs and provide effective protection against cyberattacks.
First of all, the security capabilities of a firewall should be your main concern when choosing the firewall. Packet filtering is a must to mitigate risks and analyze data packets properly. But what a packet-filtering firewall is? Basically, the firewall divides any incoming data into smaller packets and evaluates it based on pre-defined rules. Then it decides if it’s allowed or not.
Scalability is another important factor. As your organization grows, your firewall solution should be capable of meeting the new business requirements as well as serving new users seamlessly.
Finally, think about the simplicity of management and updates. A user-friendly interface and automated updating methods add to your firewall solution’s long-term durability.
Assessing Firewall Providers: Trust and Support Considerations
When choosing your firewall provider, you need to go beyond their product and check their track record. Remember, you’ll be working with them the whole time so you need to ensure they are reputable and trustable.
Begin by investigating the firewall provider’s reputation and track record. Look for well-known industry brands with a track record of providing efficient solutions. Client testimonials and industry awards might provide useful information about the provider’s performance and client happiness.
In cybersecurity, dependable customer support is critical. Examine the customer service channels, response times, and availability of the provider. Service level agreements (SLAs) clearly establish expectations for response times and issue solutions, providing you peace of mind when an emergency arises.
Implementing Your Chosen Firewall: Best Practices
Ensuring a successful deployment process is critical for the effectiveness of your firewall. For a smooth implementation, follow these suggestions. Start by evaluating your vulnerabilities and network before deployment. Gather all your findings. Define objectives and document your firewall policies based on these findings.
Then, start by configuring the firewall following industry standard practices. Make sure to integrate your firewall with other security services such as MFA for better protection. Always keep your firewall up to date with the latest patches.
After implementation, always monitor your network for anomalies, and train the end-users on firewall usage. Conduct pen tests and vulnerability scans frequently, document the insights, and continuously optimize firewall policies based on them.
Firewall Testing and Troubleshooting: Ensuring Optimal Performance
Once the implementation process is over, it’s essential to test and troubleshoot the firewall. Simulate potential attacks on your test environment to scan the firewall for vulnerabilities. Check out the weak points and reinforce them promptly.
In the event of an anomaly, a proper troubleshooting plan will come into play. If you have a structured approach for troubleshooting, you can investigate and diagnose the incident quickly, and respond accordingly. You can also leverage firewall logs for troubleshooting as they give you an idea of why a problem might have occurred.
Maintaining Your Firewall: Regular Updates and Reviews
Firewalls are meant to be always updated and reviewed by professionals. This is because threats are not static, and they are evolving. If you combine all the insights you gather from troubleshooting and vulnerability scans, you’ll be able to understand what are the new threats awaiting your network and implement necessary measures for them.
If you are using a software firewall, meaning if you get the service from a third-party, always look for available updates. Any update on firewall software will mean that the developer team found something they need to patch, and you need to update the software on your device before attackers exploit it. Remember, these vendors have expert teams searching for vulnerabilities, and they send regular security patches to their clients.
